Security
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Enterprise-Grade Protection
Project Playbook is built on a foundation of trust and transparency. Leveraging Microsoft 365’s robust security framework—including identity management, encryption, and role-based access control—we ensure your data is protected at every layer. Deployed in your environment, Project Playbook supports full data ownership and privacy compliance with standards such as NIST, DoD, and GDPR. From secure configuration to audit readiness, our platform strengthens your security posture while meeting the highest enterprise and regulatory expectations.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
Resource Optimization
Manage capacity, demand, and utilization for all enterprise resources.
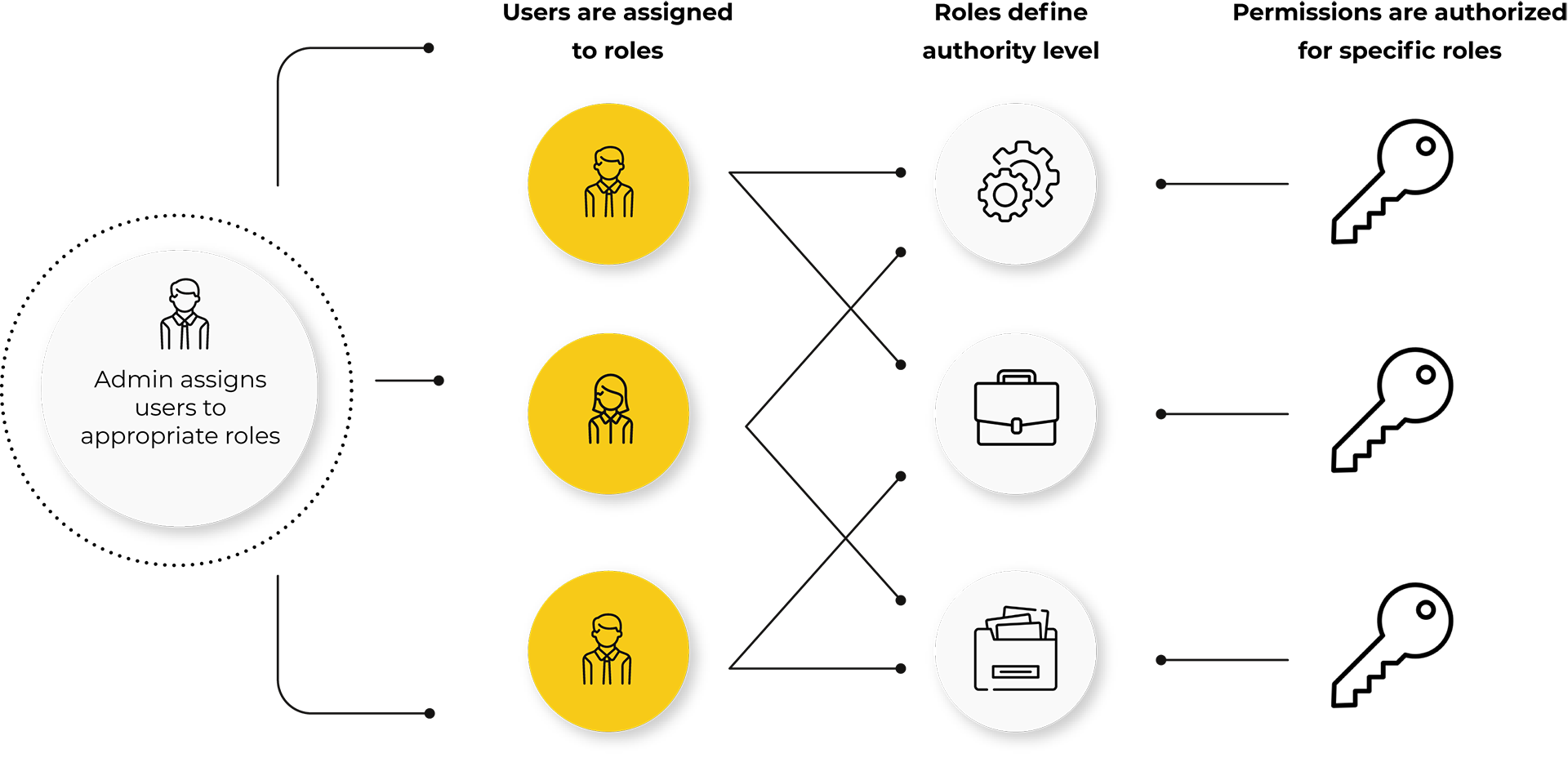
Flexible Security Model
Project Playbook features a robust, task-role-based access control system designed to protect your data while supporting your organizational complexity. Use it out of the box with our proven templates or fully tailor it to your enterprise structure. We support even the most intricate models—and provide expert consulting and change management services to ensure smooth adoption.
Security
Project Playbook is built on decades of industry best practices, applying advanced access controls, encryption, and monitoring to protect your data at all times—while enhancing your organization’s overall security posture.
Privacy
Deployed in your cloud environment, Project Playbook gives you full control over your data. We provide guidance and templates to help you implement the right security measures for your enterprise.
Compliance
Our security framework aligns with leading standards such as NIST and DoD guidelines. We follow proven protocols to ensure compliance and give you confidence that your data is managed securely.